Security: Fundamental Answers

This week, Software Engineering Daily sought answers to some fundamental questions from the following guests:
- David Schwartz talked about maintaining security in Ripple, a distributed cryptographic payment system
- Craig Smith explained the attack surfaces of cars and the consequences of the Wired Jeep hacking
- Bruce Schneier surveyed Ashley Madison and other recent events, and talked about Data and Goliath
- Max Krohn talked about verifying identities with Keybase and protecting OKCupid’s users from bots
- Adrián Lamo gave a long-time hacker’s perspective on identity, encryption, and other contemporary security topics
What is the difference between security and privacy?
“That’s an odd question,” Bruce Schneier said after I asked him this. “It’s sort of like when people ask me to define what ‘Security’ is.”
“They are two different words with completely different meanings. I’ll turn it back on you. What’s the difference between security and privacy?”
“Security is what protects your privacy” I said. Bruce said that was a pretty good answer. “Security might also give you safety” he added.
More broadly, there is a gradient of tradeoffs between security, privacy, safety, and utility.
Keybase provides safety at the expense of privacy. Every additional social account which a user connects to Keybase creates a stronger layer of identity. Keybase’s utility provides safety by adding protection from masquerade attacks.
Keybase is not the only example of utility at the expense of privacy. Facebook will provide better visibility for lenders, and we will see smarter allocation of capital.
What is different about computer security in newer areas such as cryptocurrencies, cars, and internet-of-things?
More attack surface.
Craig Smith explained how a car’s infotainment center can be hacked to take control of the car. Other car attack surfaces include USB ports, keyfobs, and Bluetooth.
As Mark Cavage says, “you are building a distributed system”, whether it is an e-commerce site or a car. The larger a distributed system is, the higher the probability one of its nodes will betray the system itself.
Ripple’s chief cryptographer David Schwartz encouraged an attitude of humility in the face of complex security problems. “Don’t try to do too much.”
In Ripple, distributed systems theory is no match for reality.
Schwartz said that academic theory often makes assumptions that don’t work in the real world.
In much of the distributed systems theory, the nodes have to know who they are dealing with from the start, “which for Ripple is a non-starter.”
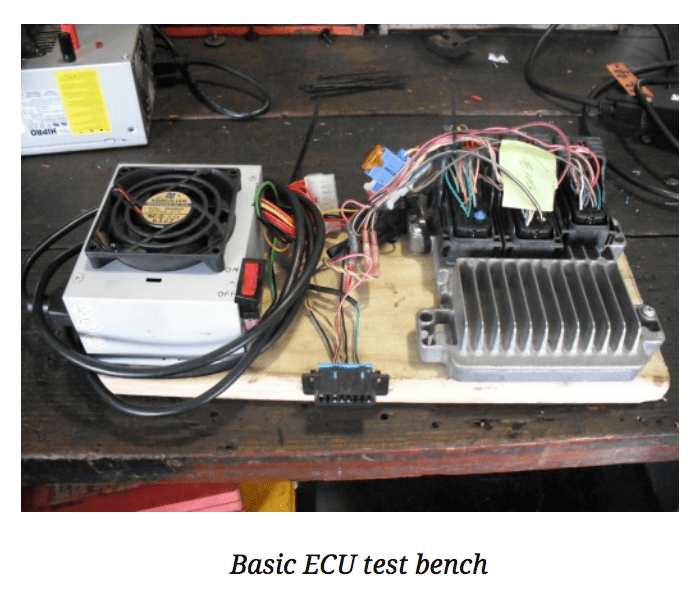
Simulation is important in both Ripple and car security. Ripple simulates millions of edge-case scenarios in its effort to create a highly resilient transaction system.
Car hackers go to junk yards to construct cheap simulation stations.
What themes recur during Security Week?
A decentralized future will require a path with gradually less centralization. Blockchain protocols decrease the need for central authority like lightbulbs decreased the need for torches.
Even after the lightbulb was created, wiring up the world with electricity took a lot of work.
Similarly, moving towards a decentralized blockchain ideal requires effort, both technological and societal.
My Ethereum skepticism was not rooted in a belief that Ethereum is a bad idea. I fear Ethereum may be trying to do too much, too soon.
Ripple is the target of more skepticism than Ethereum. But Ripple is realistic. Ethereum wants to boil the ocean of centralization.
“Having a currency without a government backing it up is risky” said Bruce Schneier. Ripple is a blockchain value transfer system for which banks are the early users. It is a stepping stone of semi-centralization.
Ripple critics also gripe about the large amount of XRP held by Ripple Labs, centralizing its development. This is a feature and not a bug. Open-source ecosystems tend to benefit hugely from a highly invested benefactor.
Encryption works. Bruce Schneier emphasizes this in a talk he gave at Google. Adrian Lamo has been consistently using encryption for decades. The government’s absurd efforts at limiting encryption is the starkest evidence of encryption’s effectiveness.
Keybase is an open-source, decentralized identity system. A user of Keybase can add a cryptographic keys associated with social media accounts. These keys create a web of trust for an individual that asymptotes towards incontrovertible identity.
Keybase recently raised $10.8 million to make encryption usable.
What are the individual lessons to take away from recent watershed security events, namely Ashley Madison, the Jeep hacking, the fall of Mt. Gox, Stuxnet, and the Snowden disclosures?
Ashley Madison: The security community is taking this opportunity to say “if you aren’t careful, this could be you.” The Ashley Madison case is not unique in the volume damage it inflicted on victims, but it is unique in its mediagenic salaciousness.
Wired Jeep hacking: Cars are extremely vulnerable and laden with attack surfaces. Also, the media craves salacious stories so badly, it will risk lives to create them. Craig Smith was rightly critical of Wired‘s approach: stopping a car on a busy highway.
Fall of Mt. Gox: Centralization leads to fragility. Bruce Schneier pointed out that with new decentralized systems, we rarely see problems with the technology of the systems themselves. We see problems in the people and infrastructure built around them.
Stuxnet: Nation-states are capable of deft cyberattack. The team behind Stuxnet showed strong attention-to-detail. Also, international cyberwarfare is exceedingly difficult to attribute. Regarding Stuxnet, this is outlined in Countdown to Zero Day.
Snowden: there is no opting out of the security dragnet. Schneier’s goliath is embodied in corporations and governments. My personal opinion: it is better to leverage the tools goliath offers in exchange for your data than to try to hide. Example: Facebook is a fantastic utility for self-expression. When people choose not to use it for fear of giving away data, I wonder if they realize how much they are limiting their own creation of new, unique data.